T
Lumara in Action
Lumara in Action: How We Stopped a Network Scan No Endpoint Tool Could See

What does a student with Kali VM find when they scan 673 IP addresses on an Australian school's internal network? Nothing useful. Every cross-VLAN probe was denied by default at the firewall. Our SOC traced the source, called the school, and had the device off the network sixteen minutes after the first alert.
Most organisations trust their segmentation to hold against this kind of probe. Few have tested it. Here's what happened when one school did.
A Student Scanned 673 IPs in 30 Minutes
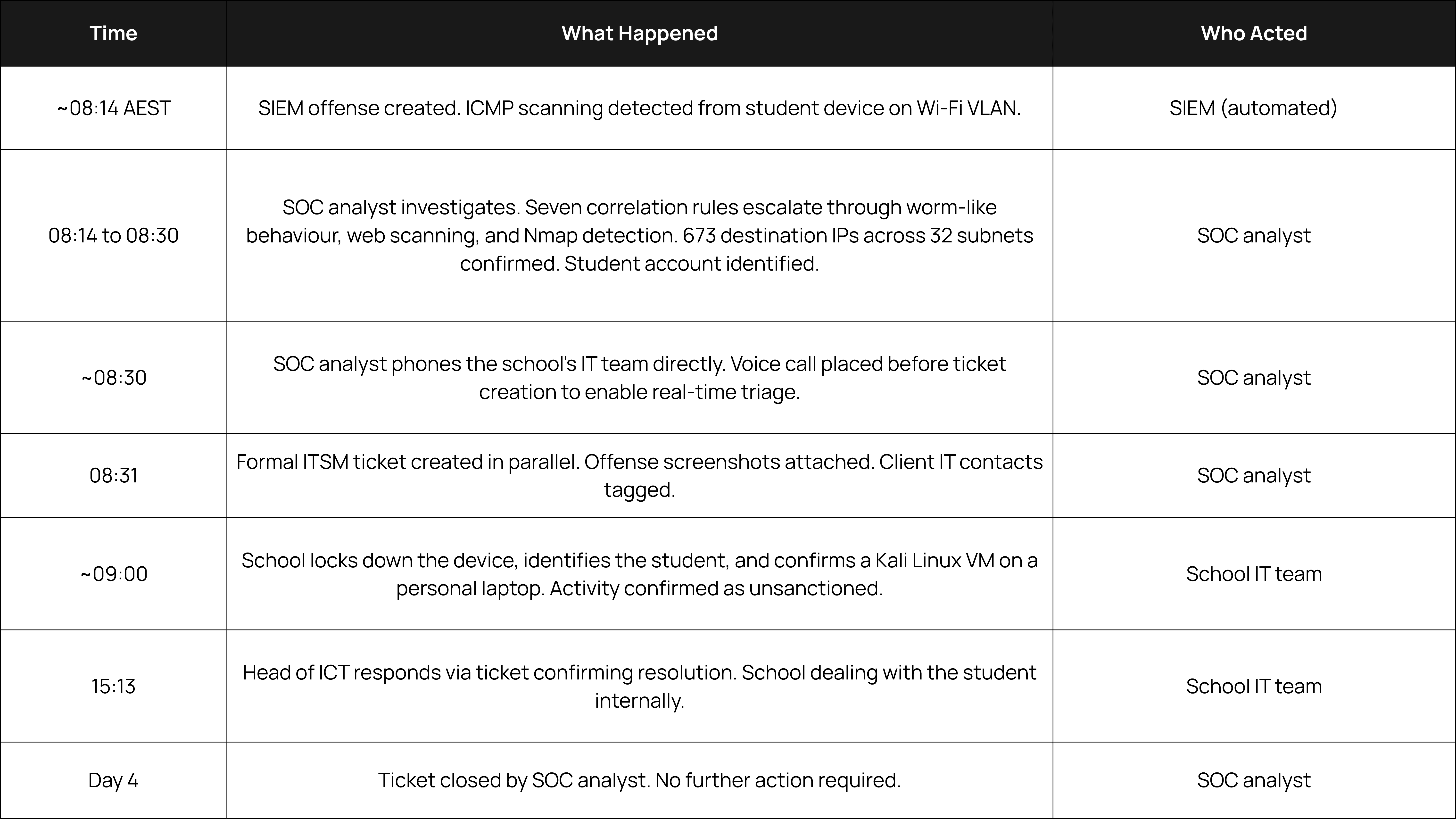
The alert came in at 8:14 on a regular school morning. A device on the student Wi-Fi network was probing the school's internal environment across 32 network segments, generating 1,662 events in half an hour.
Seven SIEM correlation rules fired within minutes: ICMP scanning, suspicious probes, worm-like behaviour, web scanning, mass firewall denials, and confirmed Nmap reconnaissance. When our team traced the source, it turned out to be a student-owned laptop running a Kali virtual machine.
Our SOC analysts watched the alerts build and called the school's IT team directly at 8:30 AM, just 16 minutes after the first alert. The activity was aggressive, and waiting to write a formal ticket would have cost critical response time if the student's account was compromised.
The school confirmed the activity wasn't sanctioned, locked the device immediately, and identified the student. The formal ticket followed at 8:31 AM with documentation running in parallel with the response. By the end of the school day, the case was closed.
The Network Held
The student tried to reach 673 IP addresses across 32 subnets. The firewall denied nearly every one of those connections outright. Student Wi-Fi was classified as untrusted, and deny-by-default rules blocked cross-VLAN traffic from touching the server network or other critical infrastructure.
Without those rules, this scan could have moved past reconnaissance into service enumeration and OS fingerprinting across the school's entire environment. Instead, the firewall logged every denied attempt, the SIEM correlated those denials into a clear picture, and the SOC acted before the student achieved anything.
Here is what held up and why it matters:
Network segmentation: Untrusted VLANs were isolated from critical infrastructure, with cross-subnet traffic routed through a next-generation firewall with deny-by-default rules. This stopped the scan from reaching its targets.
SIEM correlation: Seven rules fired across four log sources, assembling a complete picture of the activity within minutes. The correlation engine built the story from multiple independent signals, rather than relying on a single data point.
Human speed: Our analyst called the client before writing the ticket. The school's IT team had actionable intelligence in real time.
Client readiness: The school acted on the spot to lock the device and identify the user, resolving the case the same day.
This wasn't a new defence strategy. It was foundational security, configured correctly and monitored.
The Device Was Invisible to Us
There is a critical detail in this incident: we had zero visibility on the scanning device itself.
Because there was no endpoint agent or telemetry installed, the student's personal laptop was invisible to our monitoring. Every piece of evidence came from the impact that scan had on the infrastructure around it: firewall session denials, Windows Filtering Platform blocks on destination hosts, and the SIEM correlation that connected those events.
In a BYOD environment, an XDR agent won't be on every student laptop or visitor's phone. What can be controlled is what those devices are allowed to reach, and whether the infrastructure around them is watching closely enough to catch unusual behaviour.
When the device posing the risk is the invisible one, security depends entirely on the controls around it. Without strict segmentation and cross-subnet monitoring, a device like this could move through a network quietly.
Any Guest Network Carries the Same Risk
This happened at a school, but the principle applies to any organisation that gives network access to people it doesn't fully manage.
Think about a council library offering public Wi-Fi alongside internal administrative systems, or an Australian business bringing in external contractors who connect their own devices. It's the same story for corporate guest networks that aren't properly segmented from production systems, or state government offices where visitors connect to shared Wi-Fi every day.
If untrusted users can reach trusted systems, the exposure is the same. And the threat isn't limited to curious students. What if those credentials had been stolen through phishing, and a capable threat actor was behind that device? A more experienced attacker wouldn't scan 673 IPs in one burst. They would probe a handful of targets, wait a few hours, probe a few more, and spread the activity across weeks. That patience makes detection much harder.
The controls that stopped this student are the exact same controls that contain that kind of threat: strict network segmentation and deny-by-default firewall rules. This school had them and they held. The question is whether yours would.
Most Environments Would Miss This
If a device on your network started scanning 673 IP addresses tomorrow morning, what would the next 16 minutes look like?
Without someone watching in real time, those alerts sit in a queue. By the time an internal team reviews them, an attacker has already moved laterally.
For this school, the threat was neutralised before the first bell. Proactive segmentation stopped the scan from reaching critical servers, our SIEM correlated the scattered logs into a clear narrative within minutes, and our 24/7 SOC acted on it immediately, calling the school directly with the intelligence they needed to lock the device down.
Lumara combines SIEM correlation and 24/7 SOC monitoring so threats like this are caught and contained in minutes. See how it works for your environment.

